Effortless Compliance, Accelerated.
Get Certified in Weeks, Not Months.
Qalea unifies cybersecurity and compliance so you can move faster, stay protected, and get certified with ease.



Qalea keeps your business secure and compliant effortlessly.
Our platform unifies cybersecurity, compliance, and integrations, delivering continuous protection and actionable insights, ready to plug straight into your operations.

.jpg)




Qalea centralizes all certification requirements and controls in one dashboard. Track progress, generate evidence automatically, and stay always audit-ready.

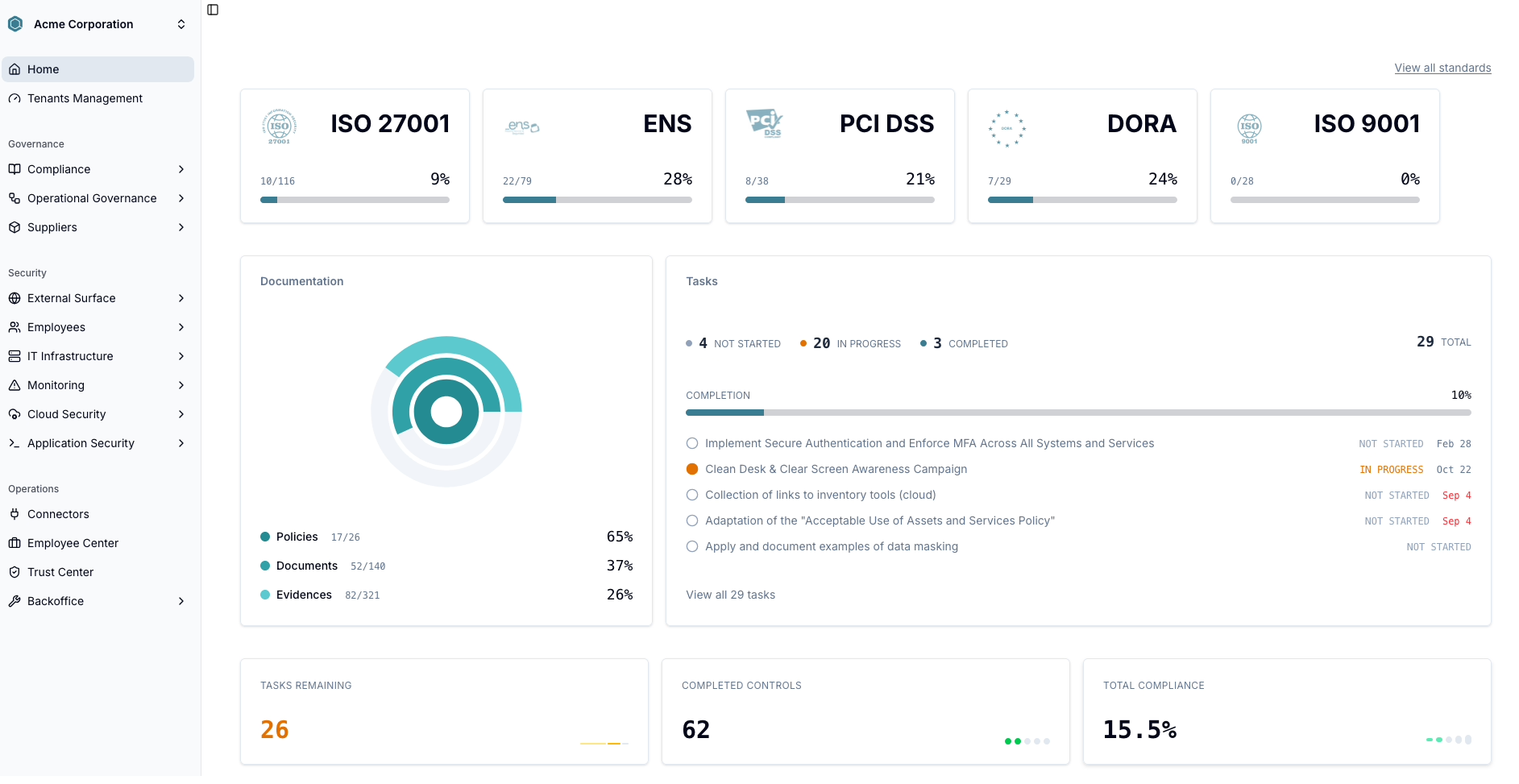
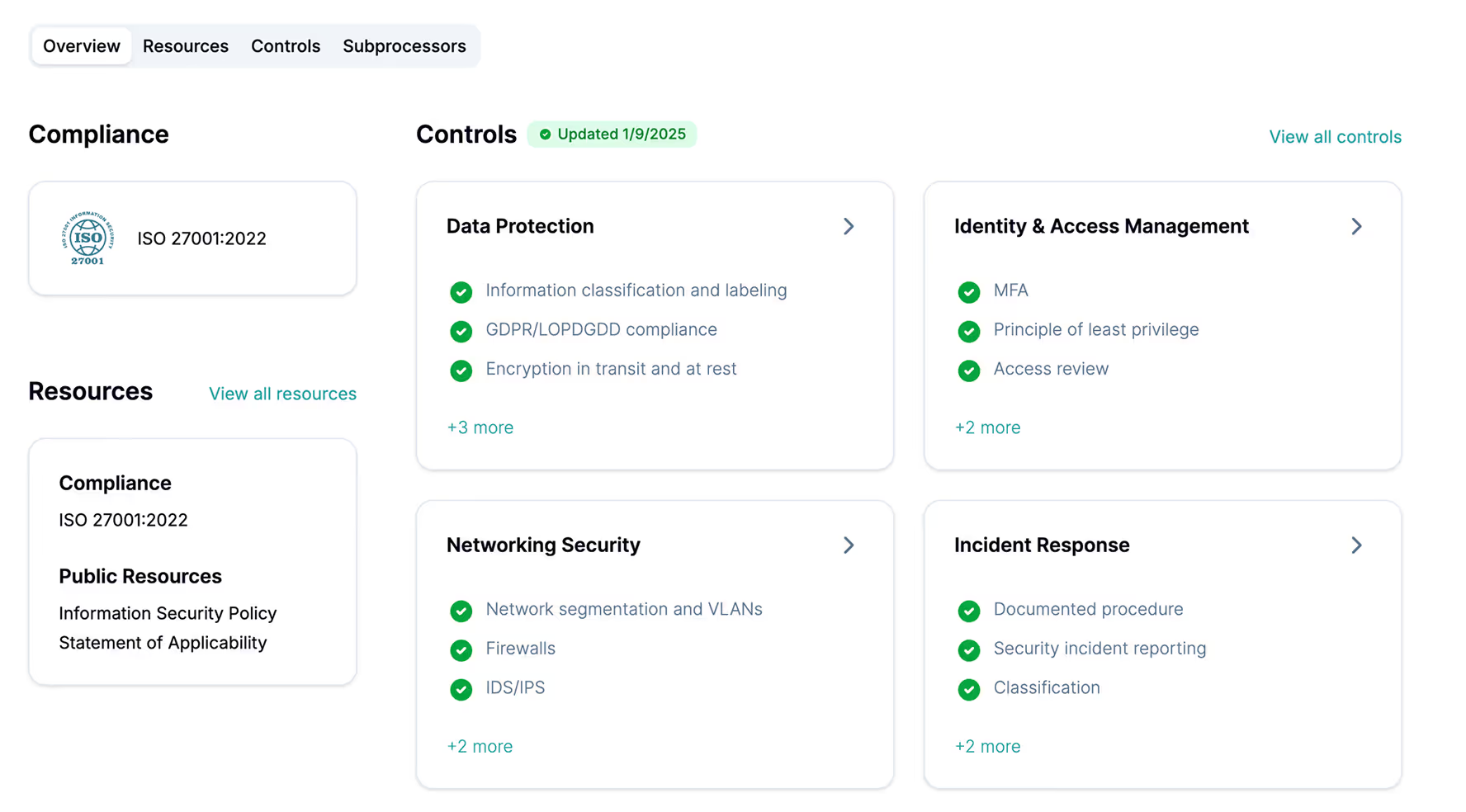
Show your compliance status in real time with trust center.

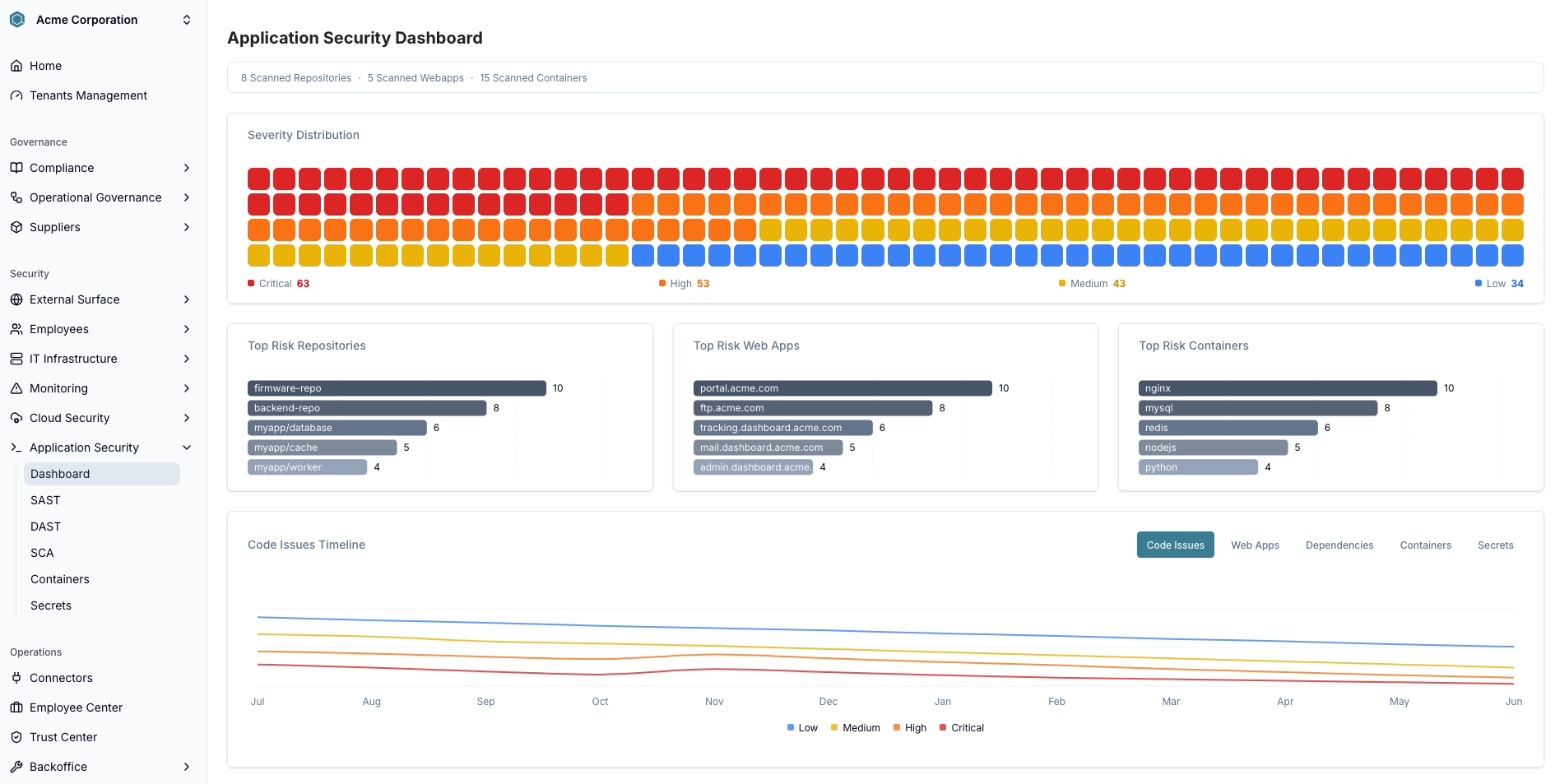
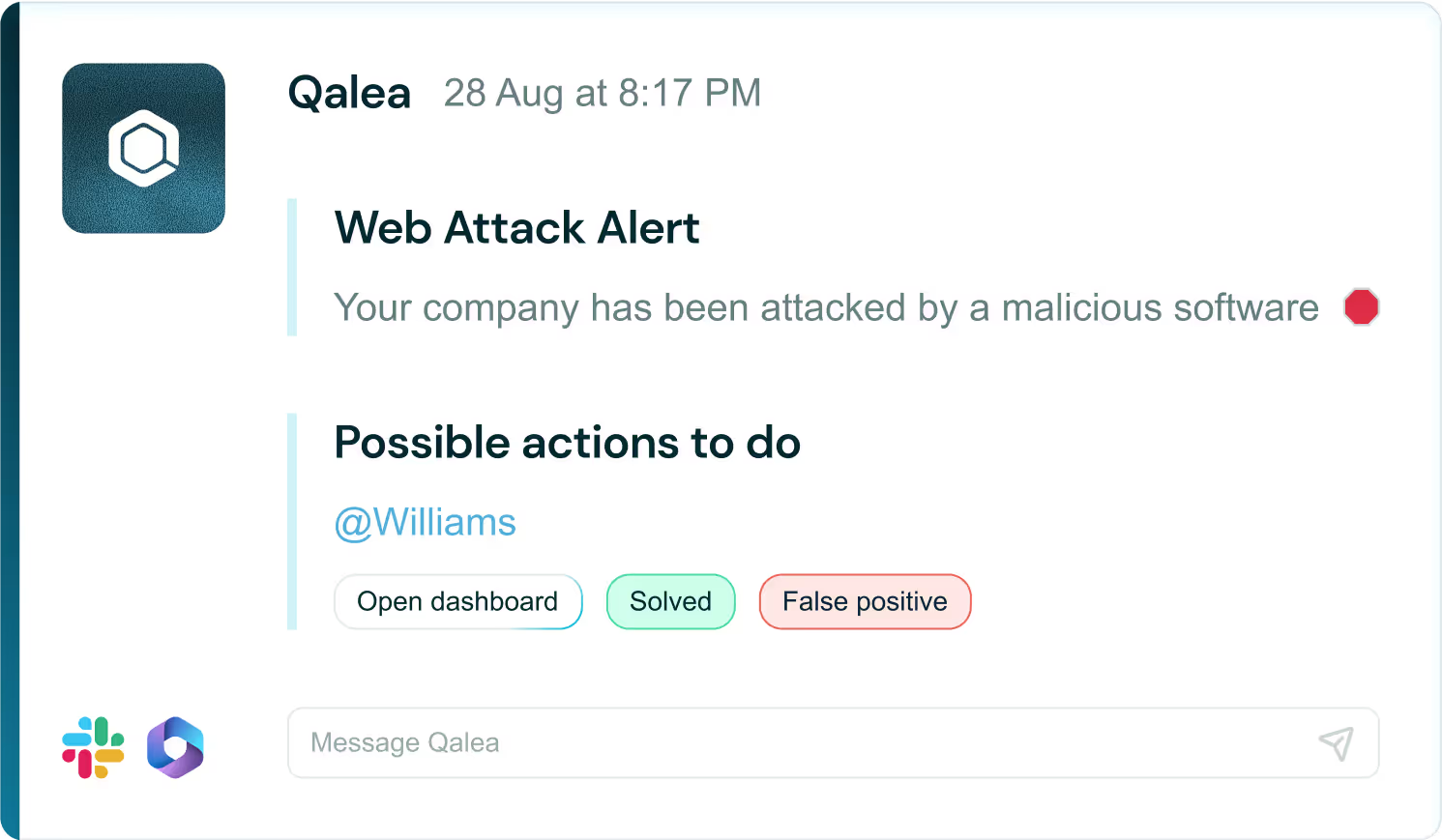
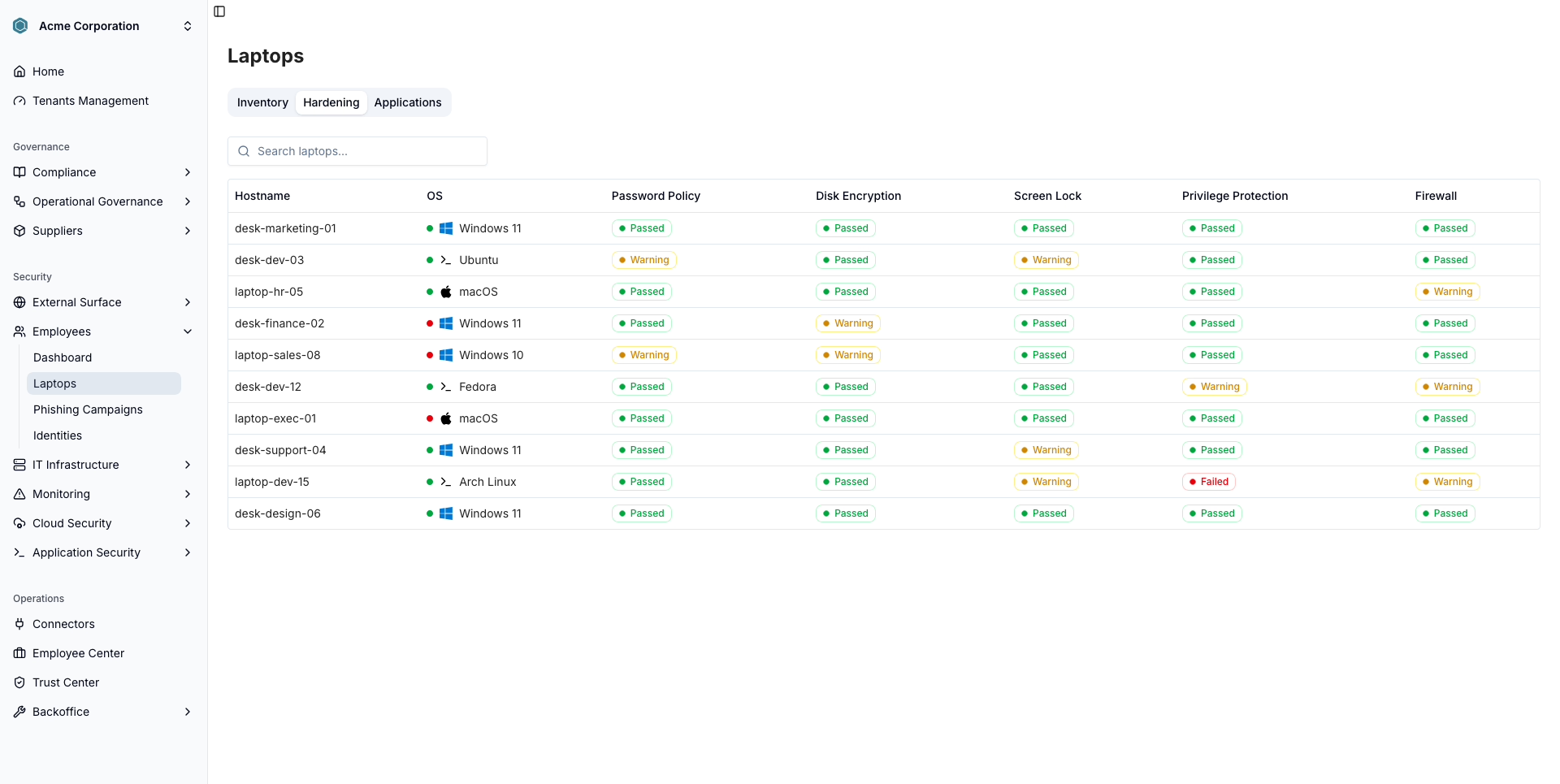
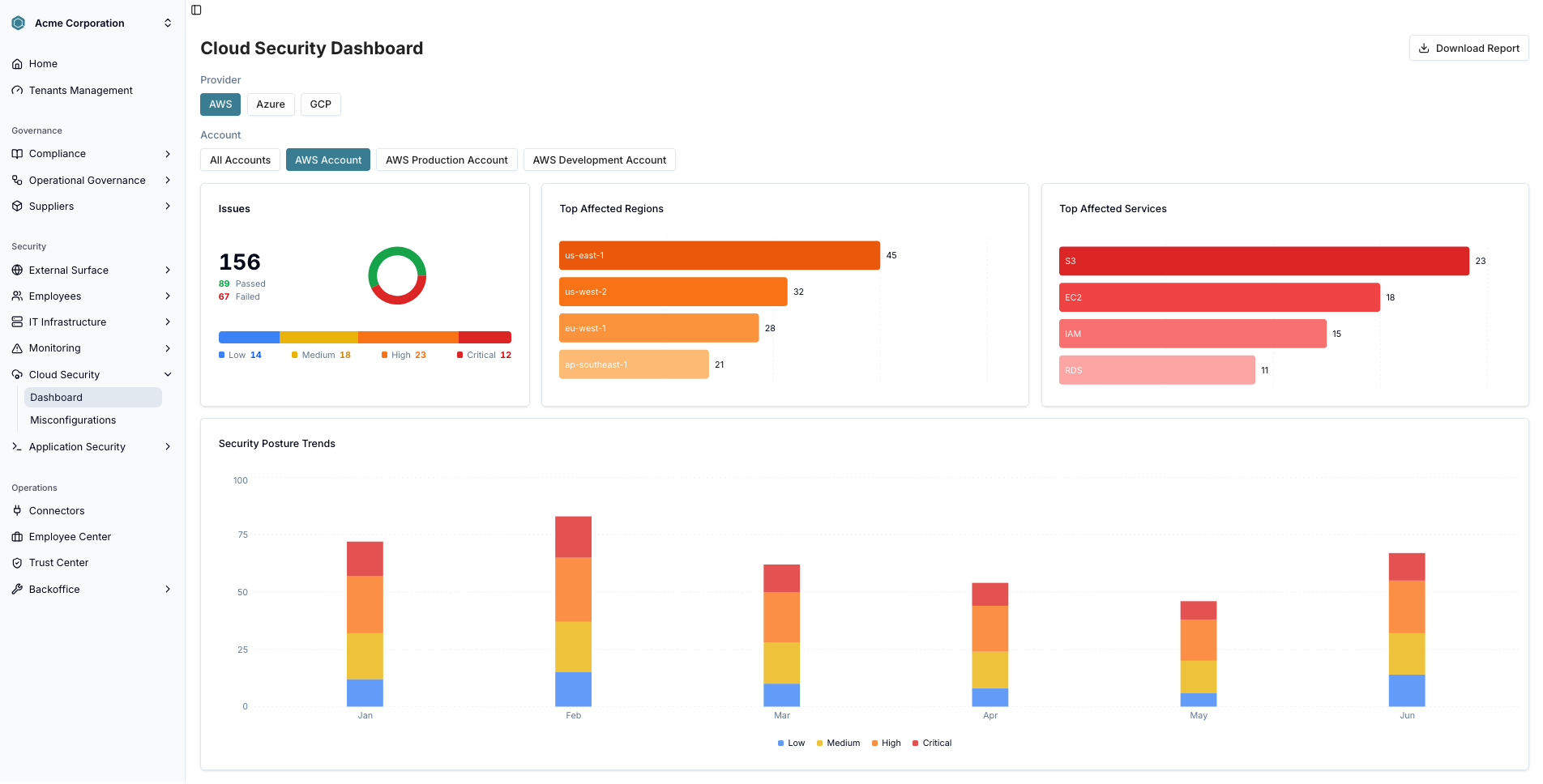
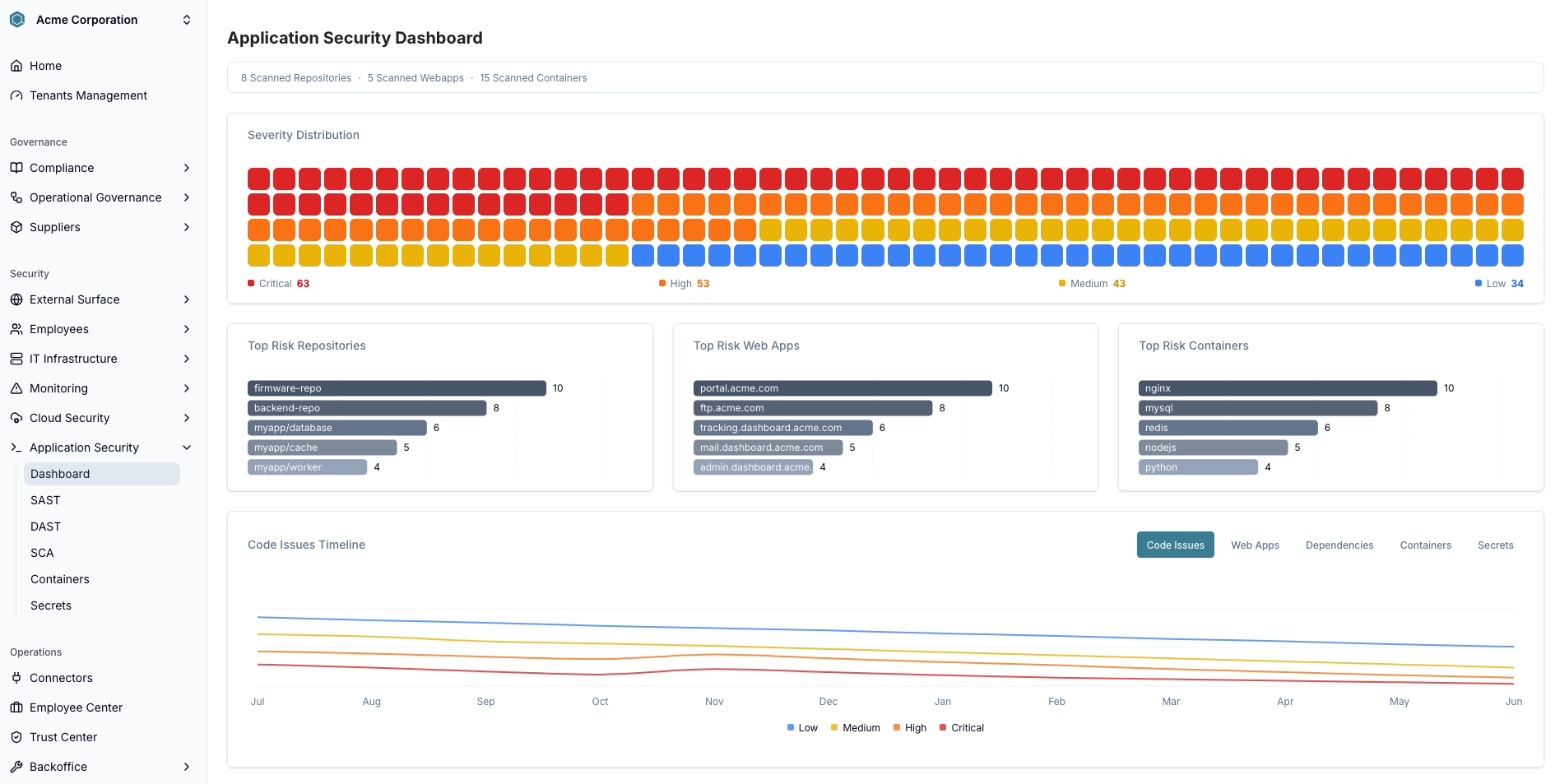
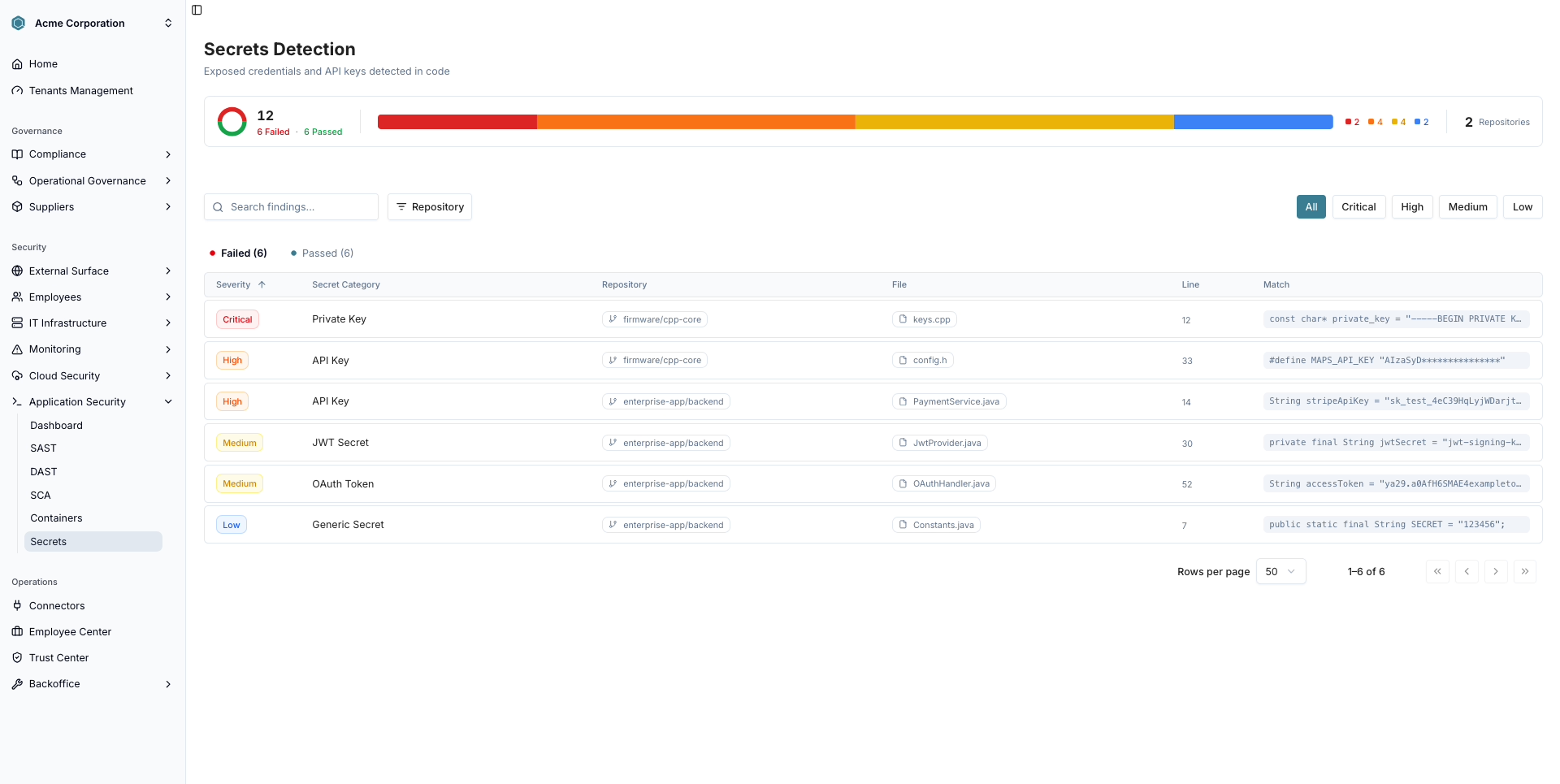
A continuous security dashboard that monitors vulnerabilities, access, and critical configurations. Get proactive alerts and fix risks before they become incidents.

trust Qalea
Achieve the certifications your business needs, effortlessly
ISO 27001, SOC 2, HIPAA, and more – achieve the standards your business needs with confidence and speed.
















Qalea maps and applies required controls automatically, reducing manual work and accelerating your compliance process effortlessly.
Stay audit-ready at all times with real-time compliance tracking and proactive alerts for any potential risks or gaps.
Generate required documentation and evidence in minutes, simplifying external audits and ensuring a smooth certification process.
Protect every layer of your business with a complete security stack












































Connect your favorite tools
Shape Qalea around your needs with powerful tools and trusted data providers.
Everything you need to know about Qalea
Leave us your data and we will get in contact with you shortly.